MFA Setup¶
Multi-Factor Authentication (MFA) adds an extra layer of security to your Vincenty account. This guide covers setting up each available MFA method.
Overview¶
Vincenty supports three MFA methods:
| Method | Description | Best For |
|---|---|---|
| Authenticator App (TOTP) | Time-based codes from apps like Google Authenticator | Most users -- works on any phone |
| Security Keys & Passkeys (WebAuthn) | Hardware keys (YubiKey) or biometrics (Touch ID, Windows Hello) | High security or passwordless login |
| Recovery Codes | 8 one-time backup codes | Emergency access when other methods are unavailable |
You can enable multiple methods simultaneously. Recovery codes are automatically generated when you set up your first MFA method.
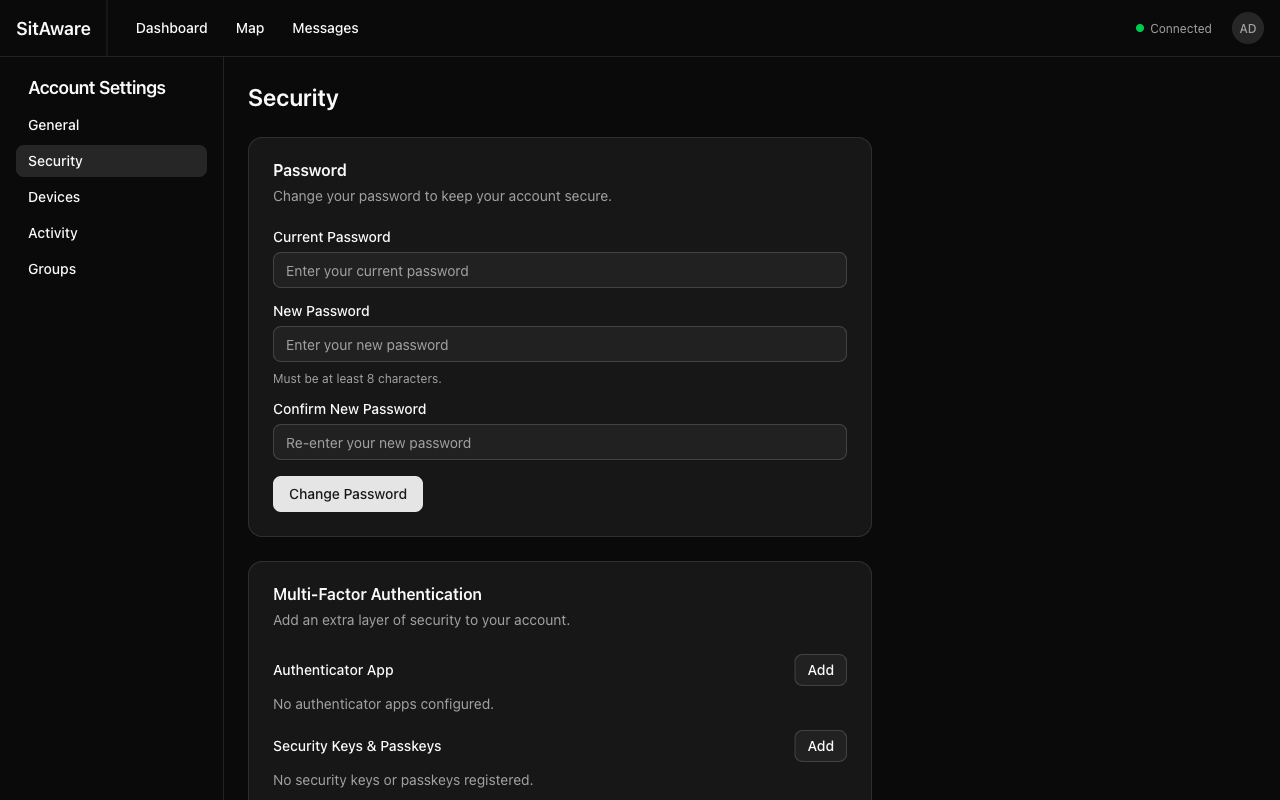
Accessing MFA Settings¶
- Click your avatar in the top-right corner of the navigation bar.
- Select Account Settings.
- Click Security in the left sidebar.
Setting Up an Authenticator App (TOTP)¶
- In the Multi-Factor Authentication section, find Authenticator App and click Add.
- A QR code will appear on screen.
- Open your authenticator app (Google Authenticator, Authy, 1Password, Microsoft Authenticator, etc.) and scan the QR code.
- The app will generate a 6-digit code that changes every 30 seconds.
- Enter the current code in the verification field and click Verify.
- If this is your first MFA method, you will receive 8 recovery codes. Save these immediately -- they are shown only once.
Using TOTP to Sign In¶
- Enter your username and password as usual.
- When prompted, open your authenticator app and enter the current 6-digit code.
- Click Verify to complete sign-in.
Removing TOTP¶
- Go to Account Settings > Security.
- In the Authenticator App section, click Remove.
- Confirm the removal.
Warning: If TOTP is your only MFA method and you remove it, MFA will be disabled on your account. If the server requires MFA, you will be forced to set it up again immediately.
Setting Up a Security Key or Passkey (WebAuthn)¶
- In the Security Keys & Passkeys section, click Add.
- Your browser will prompt you to use a security key or biometric:
- Security Key: Insert your YubiKey or other FIDO2 key and tap it
- Touch ID / Windows Hello: Use your fingerprint or face
- Passkey: Your browser may offer to create a passkey synced across your devices
- Give the credential a descriptive name (e.g., "YubiKey 5", "MacBook Touch ID").
- The credential is registered and ready to use.
Enabling Passwordless Login (Passkeys)¶
If your credential supports discoverable credentials (passkeys), you can enable passwordless login:
- After registering the credential, find it in the Security Keys & Passkeys list.
- Toggle the Passwordless option.
- Now you can sign in from the login page by clicking Sign in with Passkey -- no username or password required.
iOS (Face ID / Touch ID)¶
The iOS app has native support for passkeys and WebAuthn:
- Passkey login: Tap Sign in with Passkey on the login screen. iOS will present a Face ID or Touch ID prompt. No username or password is needed.
- WebAuthn MFA: When prompted for MFA after a password login, select the WebAuthn option. Face ID or Touch ID authenticates automatically.
- Credential registration: In Settings > Security > Security Keys & Passkeys, tap Add to register a new credential using Face ID or Touch ID.
Passkeys created on iOS are synced via iCloud Keychain and work across your Apple devices. For passkeys to work in production, the server's WEBAUTHN_RP_ID domain must be listed in the app's Associated Domains entitlement (webcredentials:<domain>).
Using a Security Key to Sign In¶
- Enter your username and password as usual.
- When prompted, insert/activate your security key or use biometrics.
- Authentication completes automatically.
Removing a Security Key¶
- Go to Account Settings > Security.
- In the Security Keys & Passkeys section, click the delete button next to the credential.
- Confirm the removal.
Recovery Codes¶
Recovery codes are your safety net when you lose access to your authenticator app or security key.
How Recovery Codes Work¶
- 8 codes are generated when you first enable MFA
- Each code can only be used once
- Codes are bcrypt-hashed in the database -- they cannot be retrieved later
- Store them somewhere safe (password manager, printed sheet in a secure location)
Using a Recovery Code¶
- On the MFA challenge screen during login, look for a Use recovery code option.
- Enter one of your unused recovery codes.
- Sign-in completes. That code is now permanently consumed.
Regenerating Recovery Codes¶
If you have used several codes or suspect they have been compromised:
- Go to Account Settings > Security.
- Click Regenerate Recovery Codes.
- All existing codes are invalidated and 8 new codes are generated.
- Save the new codes immediately.
Server-Wide MFA Enforcement¶
Your administrator may enable a server-wide policy that requires all users to set up MFA. When this is active:
- If you log in without MFA configured, you will be redirected to the MFA setup page
- You cannot access any other feature until at least one MFA method is active
- The enforcement applies to all users, including admins
See the Admin Guide for details on enabling this policy.
Admin: Resetting a User's MFA¶
If a user loses access to all their MFA methods and recovery codes, an administrator can reset their MFA:
- Go to Server Settings > Users.
- Click the action menu (...) next to the user.
- Select Reset MFA.
- The user's TOTP methods, WebAuthn credentials, and recovery codes are all removed.
- The user can log in with just their password and set up MFA again.